root@fw-01:~# show ip route
default via 10.0.0.1 dev eth0 proto static
10.0.0.0/24 dev eth0 proto kernel scope link src 10.0.0.5
172.16.0.0/16 via 10.0.0.1 dev eth0
192.168.1.0/24 dev vlan100 proto kernel scope link
root@fw-01:~# netstat -tlnp
Proto Local Address State PID/Program
tcp 0.0.0.0:22 LISTEN 1284/sshd
tcp 0.0.0.0:443 LISTEN 2091/nginx
tcp 0.0.0.0:8443 LISTEN 3102/fortigate
root@fw-01:~# nmap -sS 192.168.1.0/24
Starting Nmap 7.94 ( https://nmap.org )
Nmap scan report for gw.internal (192.168.1.1)
PORT STATE SERVICE
22/tcp open ssh
443/tcp open https
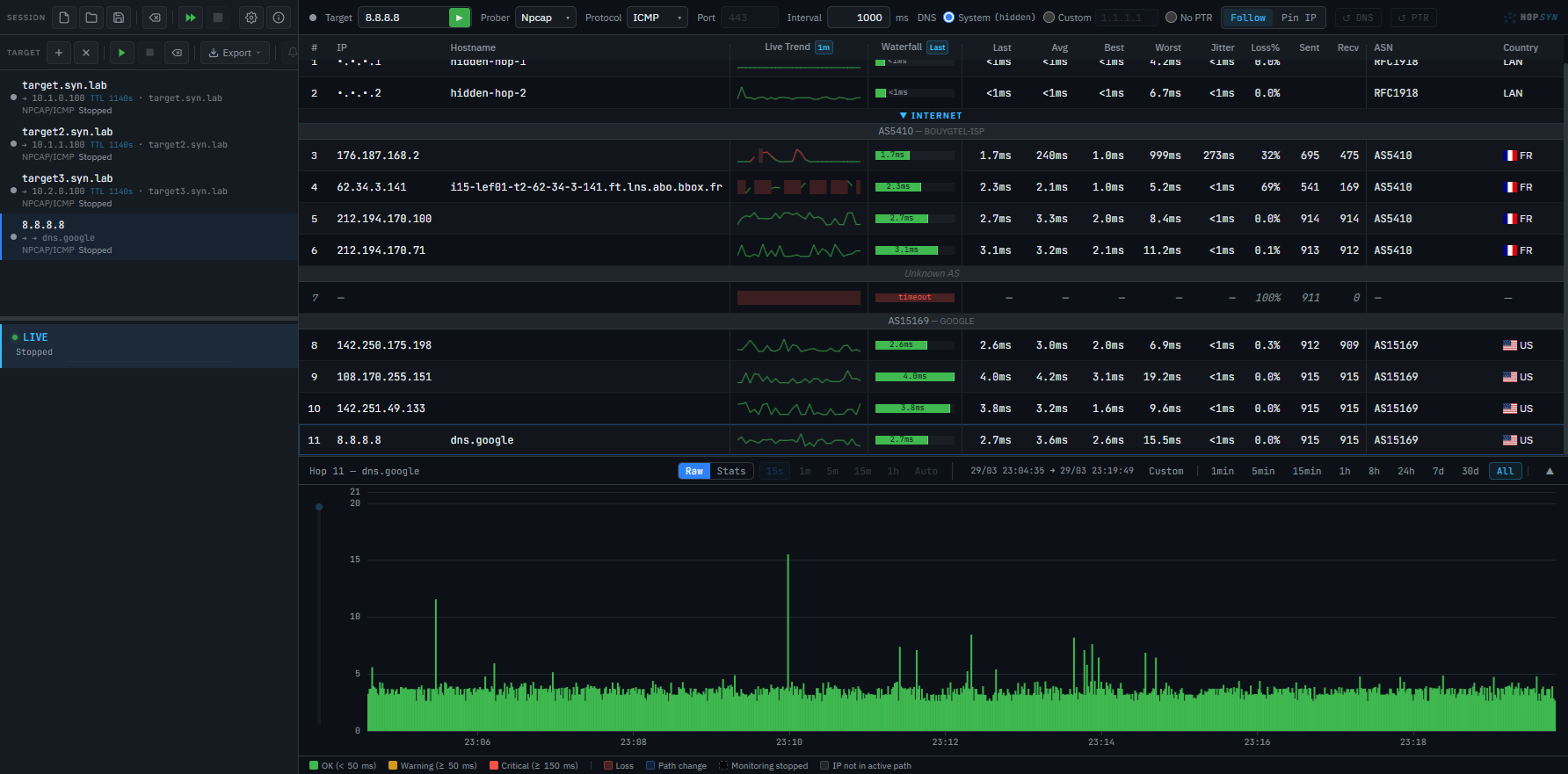
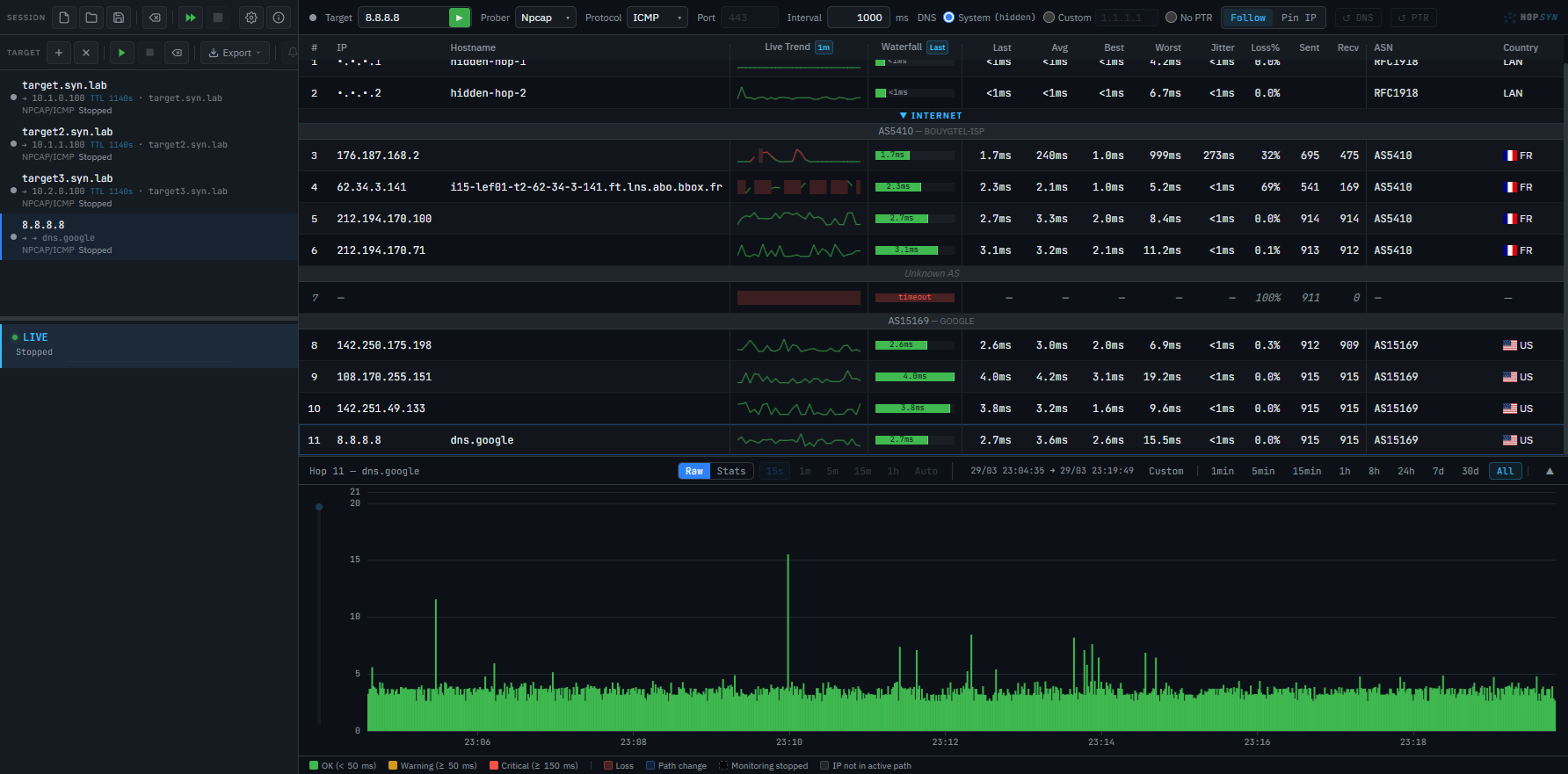
root@fw-01:~# traceroute 8.8.8.8
1 gw.internal (10.0.0.1) 0.542 ms
2 isp-pe1.par (82.65.0.1) 3.201 ms
3 core-r1.th2 (195.0.0.1) 5.672 ms
4 dns.google (8.8.8.8) 8.431 ms
root@fw-01:~# ip link show
1: lo: <LOOPBACK,UP> mtu 65536
2: eth0: <BROADCAST,MULTICAST,UP> mtu 1500
3: vlan100@eth0: <BROADCAST,UP> mtu 1500
4: wg0: <POINTOPOINT,UP> mtu 1420
root@fw-01:~# cat /etc/ipsec.conf
conn site-to-site
left=82.65.12.34
right=91.121.45.67
authby=rsasig
auto=start
root@fw-01:~# openssl x509 -noout -dates
notBefore=Jan 1 00:00:00 2025 GMT
notAfter=Dec 31 23:59:59 2026 GMT
root@fw-01:~# iptables -L -n
Chain INPUT (policy DROP)
ACCEPT all -- lo
ACCEPT tcp -- 0.0.0.0/0 dpt:443
ACCEPT tcp -- 10.0.0.0/8 dpt:22
DROP all -- 0.0.0.0/0
root@fw-01:~# bgp summary
Neighbor AS MsgRcvd State
82.65.0.1 3215 12847 Established
91.121.0.1 16276 9432 Established
root@fw-01:~# _